Configure Data Intelligence
On This Page:
Distributed Cloud Data Intelligence processes log data collected by F5 Distributed Cloud Services and uses it to equip security and fraud prevention teams with comprehensive insights into user behavior, device identification, and network data. This enables the early detection of anomalies indicative of potential security threats and fraudulent activities.
Integrate Data Intelligence with your SIEM solution or Fraud Orchestration tools and use the log data processed by Data Intelligence along with additional context and signals from your other data sources to build better rules and models and to improve the quality of data and decisions.
Data Intelligence can send log information to the following log collection systems:
- AWS S3
- Splunk
Configure Data Intelligence Data Delivery
Depending on the edition of Bot Defense that you have, there are two ways to configure Data Intelligence Data Delivery:
-
If you have Bot Defense Standard Edition, follow the instructions in the sections below to enable and configure Data Intelligence Data Delivery. To get started, see the prerequisites.
-
If you have Bot Defense Advanced Edition, you can contact your assigned Technical Account Manager for assistance enabling and configuring Data Intelligence Data Delivery. Your Technical Account Manager can perform most of the configuration process for you and guide you on how to get started with Data Intelligence Data Delivery.
You can also optionally decide to configure Data Intelligence Data Delivery yourself. To get started yourself, see the prerequisites.
Prerequisites
- You must have a valid Distributed Cloud Console account. If you do not have a valid account, see Create a Distributed Cloud Console Account.
- You must have an
Organizationplan. To see plan information, from the Distributed Cloud ConsoleHomepage, clickBilling. - You must have an externally available log collection system.
- You must add the following IP addresses to the allow list on your firewall:
- 35.247.100.206
- 34.168.102.111
- 34.168.48.1
- 34.82.248.13
- 35.230.48.185
- 35.203.143.95
Enable Data Intelligence
To use Data Intelligence, you must first enable it in the Distributed Cloud Console.
- On the Distributed Cloud Console
Homepage, clickBilling. - Click
Manage > Billing Planand scroll to theOrganization Plan. - Under the
Organization Plan, clickBot Defense. The Data Intelligence landing pages appears.Note: If Data Intelligence is already enabled, the
Data Receiverspage appears, and you can begin using Data Intelligence. - From the Data Intelligence landing page, click
Request Service.
Add a Data Receiver
Configure a data receiver to connect Distribute Cloud Services to your externally accessible log collection system.
- Log on to Data Intelligence in the Distributed Cloud Console.
- Click Manage > Data Delivery and then click Add Receiver.
- Add a
Nameto identify the new data receiver. - Optionally add a
Descriptionof the new data receiver. - From the
Data Setdrop-down menu, select the type of logs you want to send to your log collection system. - From the
Receiver Configurationdrop-down menu, select the log collection system to which you want to send log data. - To finish configuring your data receiver, see one of the following sections:
Configure an AWS S3 Receiver
-
Complete the steps in Add a Data Receiver.
-
In the
S3 Bucket Namefield, enter the exact name of the AWS S3 bucket where you want to send log data. -
From the
AWS Cloud Credentialsdrop-down list, select the cloud credentials you want Distributed Cloud Services to use to access the AWS S3 bucketIf you need to add new credentials, from the
AWS Cloud Credentialsdrop-down list, clickAdd Item. For information about adding credentials, see Cloud Credentials.Note: You must select credentials that are the AWS Programmatic Access Credentials type.
In the
AWS Regiondrop-down list, select the region where you configured your S3 storage bucket.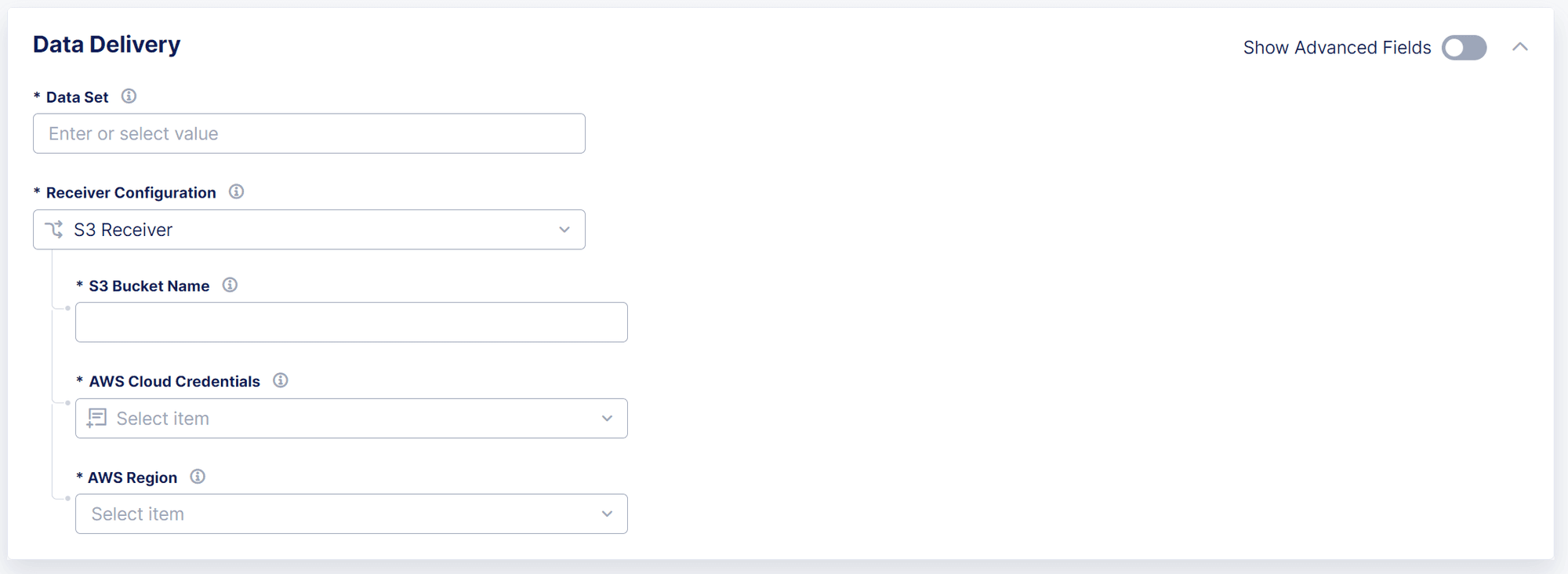
Figure: Configure an AWS S3 Receiver -
To save your AWS S3 receiver, click
Save & Continue.
Configure a Splunk Receiver
-
Complete the steps in Add a Data Receiver.
-
In the
Splunk HEC Logs Endpointfield, enter the name of the Splunk HTTP Event Collector (HEC) that you want use to send log data to your Splunk deployment.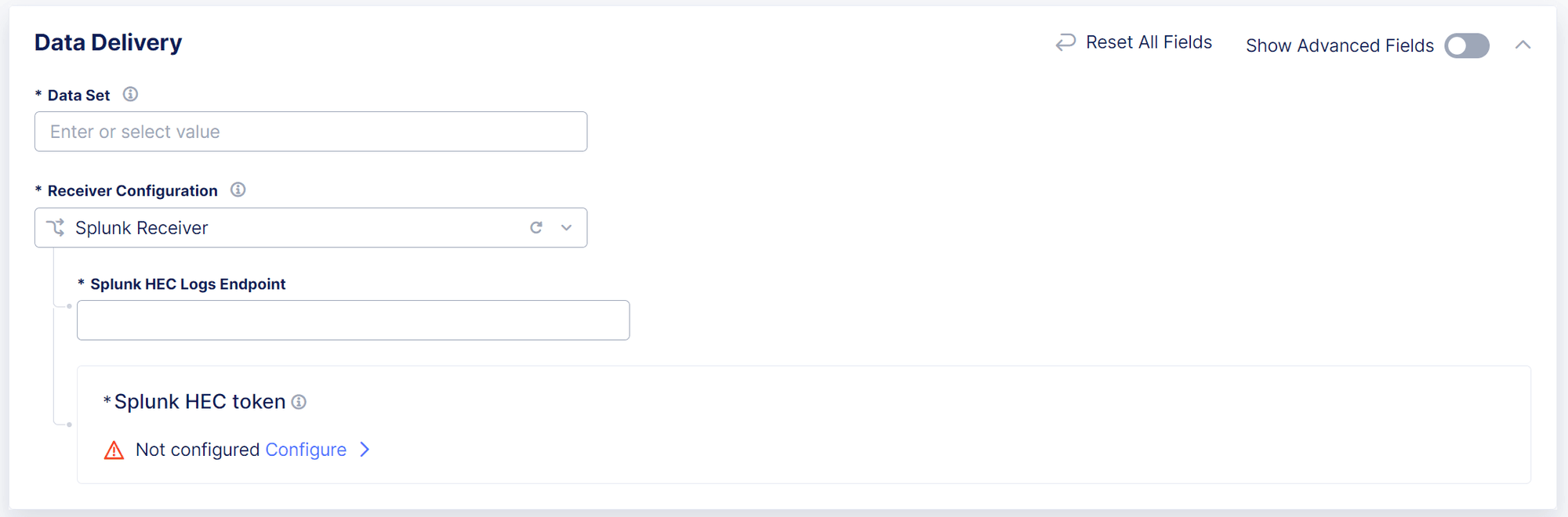
Figure: Configure a Splunk Receiver -
In the
Splunk HEC tokensection, clickConfigure. Distributed Cloud Services uses an HEC token to authenticate with the HEC. -
From the
Secret Typedrop-down list, selectBlindfolded Secret. -
From the
Actiondrop-down list, selectBlindfold New Secret. -
From the
Policy Typedrop-down list, perform one of the following actions:- Select
Built-in. - Select
Customand then select a custom policy from theCustom Policydrop-down list.
- Select
-
In the
Secret to Blindfoldfield, enter your Splunk HEC token.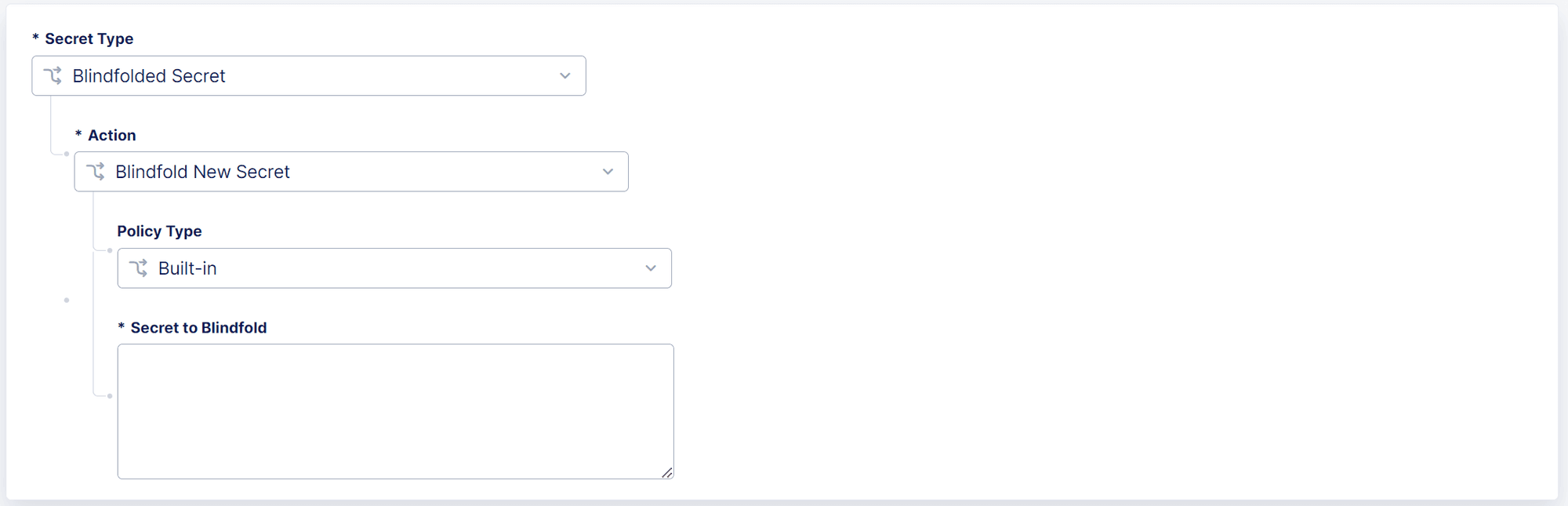
Figure: Configure a Splunk HEC Token -
Click
Apply. -
To save your Splunk receiver, click
Save & Continue.
Manage Data Receivers
Perform the following steps to manage, enable or disable, or delete existing data receivers.
Note: To add a new data receiver, see Add a Data Receiver.
- From the Data Intelligence navigation menu, click
Manage > Data Delivery. - From the list of configured data receivers, in the
Actionscolumn, click the Action menu (…) next to the data receiver you want to manage and then click one of the following options:Manage: Update data receiver configuration settings. For information about specific settings, see the following sections:Disable: Temporarily disable the data receiver that connects the Distributed Cloud Service to your log collection system. This prevents the Distributed Cloud Service from sending log data to your log collection systemEnable: Re-enable a data receiver that you previously disabled. This allows the Distributed Cloud Service to resume sending log data to your log collection systemDelete: Permanently disable and remove a configured data receiver. This cannot be undone.

