View Synthetic Monitor TLS Report
Objective
This guide provides instructions on how to review the TLS Report that is generated for HTTP(s) Synthetic Monitors. Endpoints with TLS enabled will automatically generate a TLS score along with a full report to help you quantify its current state of security.
Using the instructions provided in this document, you can navigate to and view the TLS report for a given HTTP(s) Synthetic Monitor.
Prerequisites
- A previously configured
HTTP(s) Synthetic Monitorwith TLS enabled on the monitored endpoint. If you do not have a monitor set up, see the how-to for Advanced HTTP(s) Synthetic Monitor.
Configuration
View the TLS report of a monitor
Step 1: Navigate to the monitor.
-
Log into the F5® Distributed Cloud Console.
-
Navigate to either the
Observabilityworkspace tile or menu.
Note: The homepage is role based, and your homepage may look different due to your role customization. Select
All Servicesdrop-down menu to discover all options.
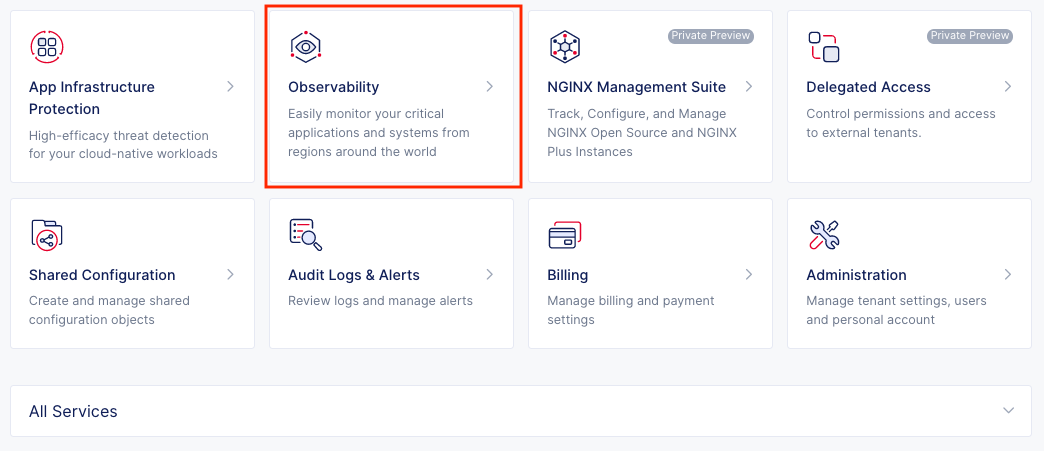
Figure: Observability Tile
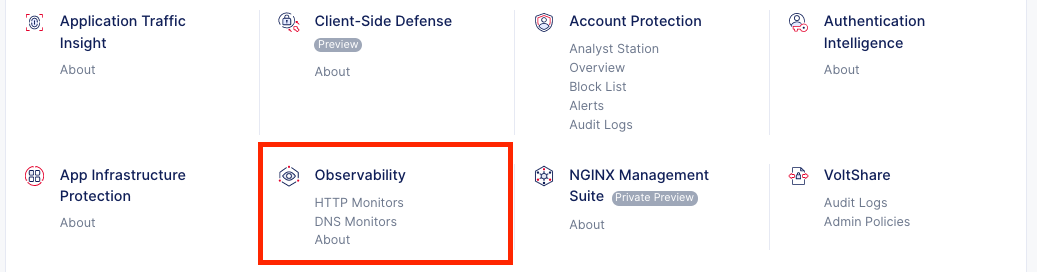
Figure: Observability Menu
-
Select
Synthetic Monitors>HTTP Monitors. -
Select the
All Monitorstab to view your monitor inventory. -
Click on the name of the monitor you would like to review the
TLS Reportfor.
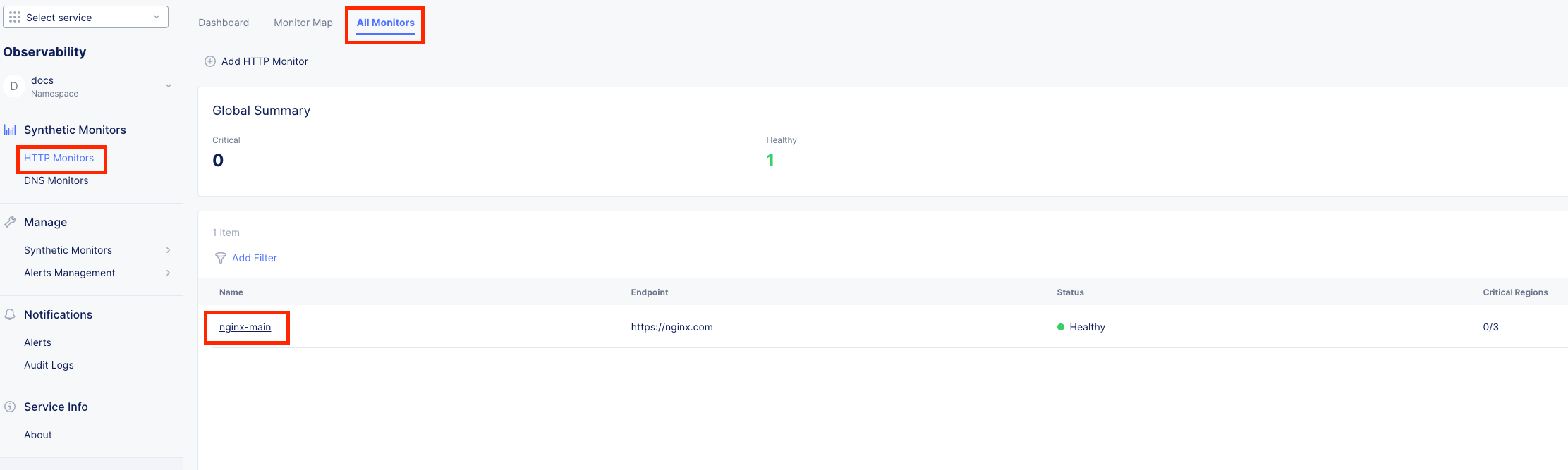
Figure: HTTP Monitor Menu
Step 2: View the TLS Summary
- Within the
Global Summarytile, you will notice aTLS Scoreto give you an overall idea of how the monitored endpoint is doing.
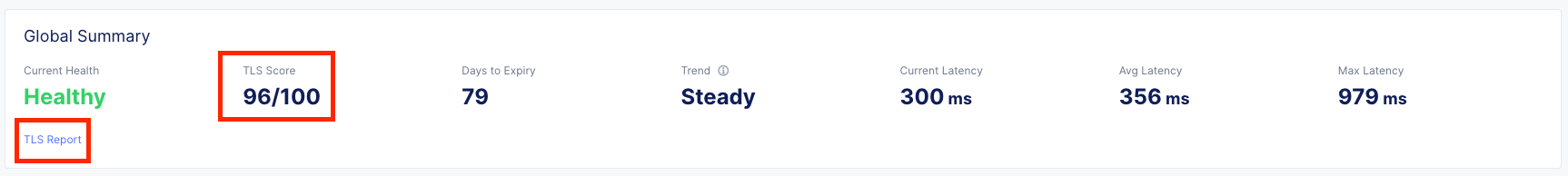
Figure: TLS Score
Step 3: View the TLS Report
-
Within the
TLS Summaryyou can open the full report in a PDF or copy it to clipboard to stick in an email or chat with your team. -
Click on
Open as PDFto view the full report.
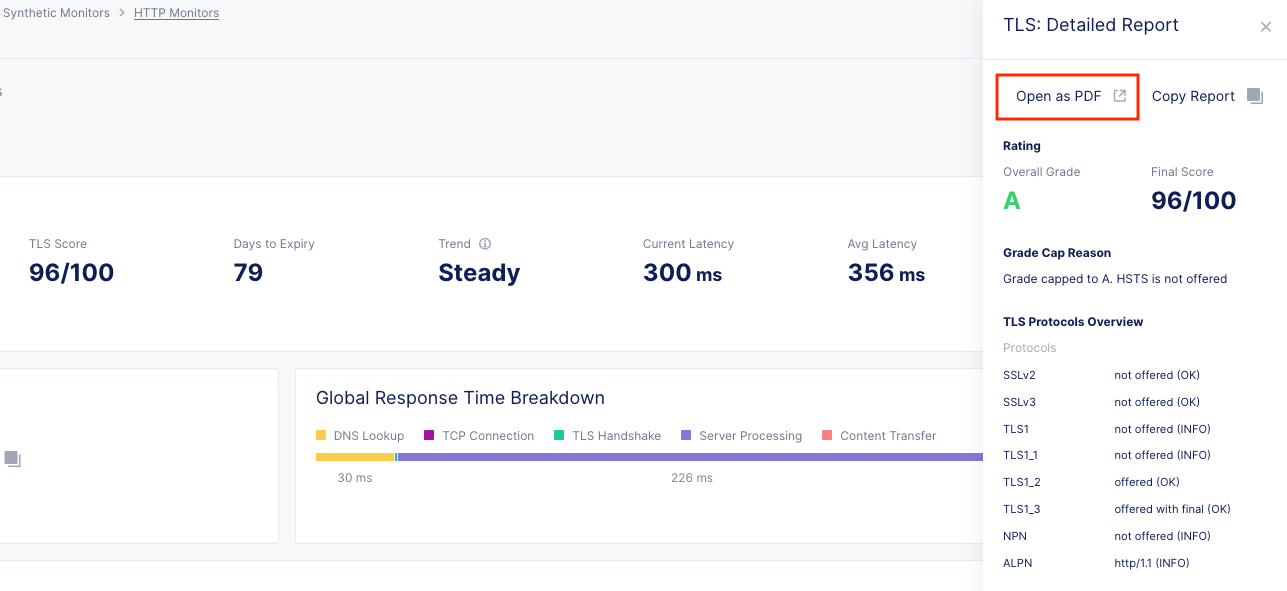
Figure: Open PDF
- Look through the report to discover configuration, vulnerabilities, and more. The example below is only a small example of what is provided.
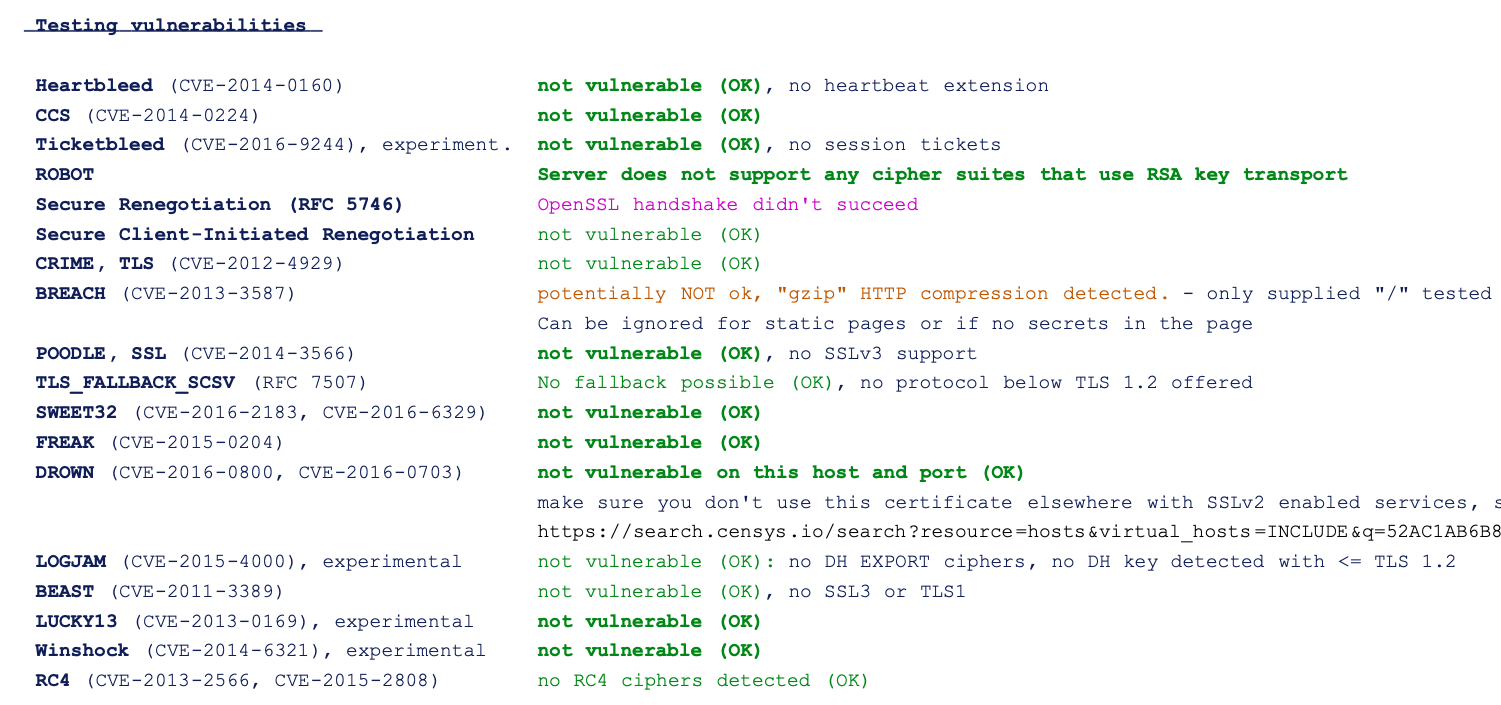
Figure: Report