Export Vulnerabilities to BIG-IP Advanced WAF
Objective
In this article, we will guide you through the process of exporting identified vulnerabilities from F5 Distributed Cloud Web App Scanning to BIG-IP Advanced WAF (AWAF) with the purpose of virtual patching by applying pre-made signature sets to vulnerable endpoints in your application(s).
Background
F5 Distributed Cloud Web App Scanning is an automated penetration testing service that scans your web applications and APIs for security vulnerabilities. Using BIG-IP Advanced WAF allows you to protect your applications from various types of attacks, including those that exploit known vulnerabilities. With this integration, you can automatically export vulnerabilities identified during a scan to BIG-IP Advanced WAF, enabling you to apply virtual patches and enhance the security of your applications.
You can use the vulnerability assessment policy template in BIG-IP Advanced WAF to create a baseline security policy and integrate it with F5 Distributed Cloud Web App Scanning. By using the output from F5 Distributed Cloud Web App Scanning, the system suggests updates to the security policy that can protect against the vulnerabilities that the tool found. You can choose which of the vulnerabilities you want the security policy to handle, retest to be sure that the security policy protects against the vulnerabilities, then enforce the security policy when you are ready.
You can find more information about BIG-IP Advanced WAF and its features in the BIG-IP Advanced WAF documentation.
Prerequisites
In order to make use of this feature, you will need the following prerequisites:
- An active F5 Distributed Cloud Services tenant with F5 Distributed Cloud Web App Scanning.
- A complete penetration test report from F5 Distributed Cloud Web App Scanning containing identified vulnerabilities.
- An active BIG-IP instance (version 14.1.0 or later) with a valid Advanced WAF license.
Exporting Vulnerabilities via the Console
To export vulnerabilities from F5 Distributed Cloud Web App Scanning to BIG-IP Advanced WAF, you need to set up an application and run an automated penetration test. Once the scan is complete, you can export the vulnerabilities to BIG-IP Advanced WAF by navigating to the report page of the completed scan and clicking on the Generate XML Export button.
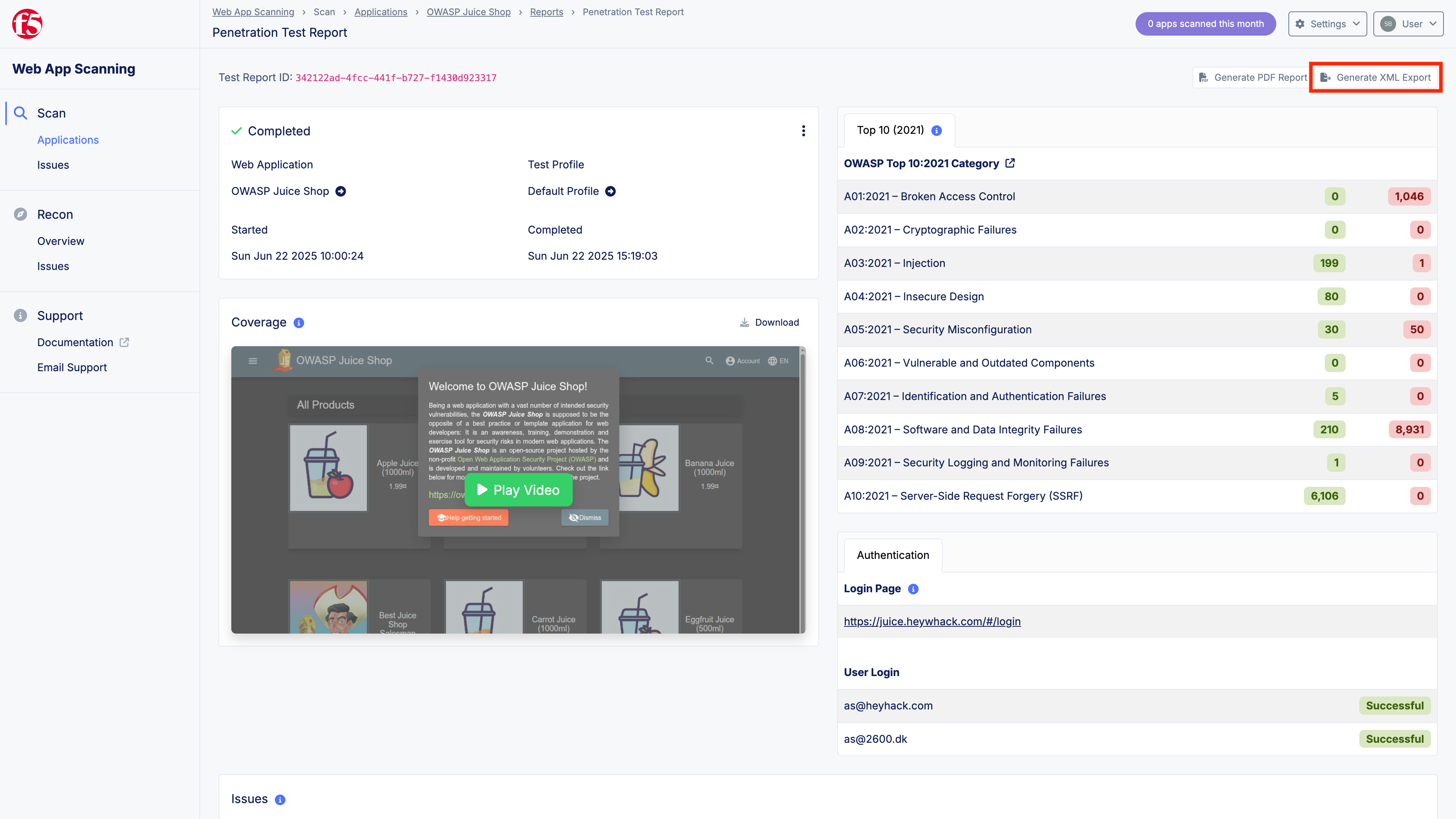
Figure: Export Vulnerabilities
This will generate an XML file containing the identified vulnerabilities, which you can then import into BIG-IP Advanced WAF. Please refer to the BIG-IP Advanced WAF documentation for detailed instructions on how to import the XML file and apply virtual patches to your security policy.
Exporting Vulnerabilities via API
To automate the export of vulnerabilities, you can use our API (documentation). The following figure describes the endpoint you can use to export vulnerabilities in the format accepted by BIG-IP Advanced WAF.
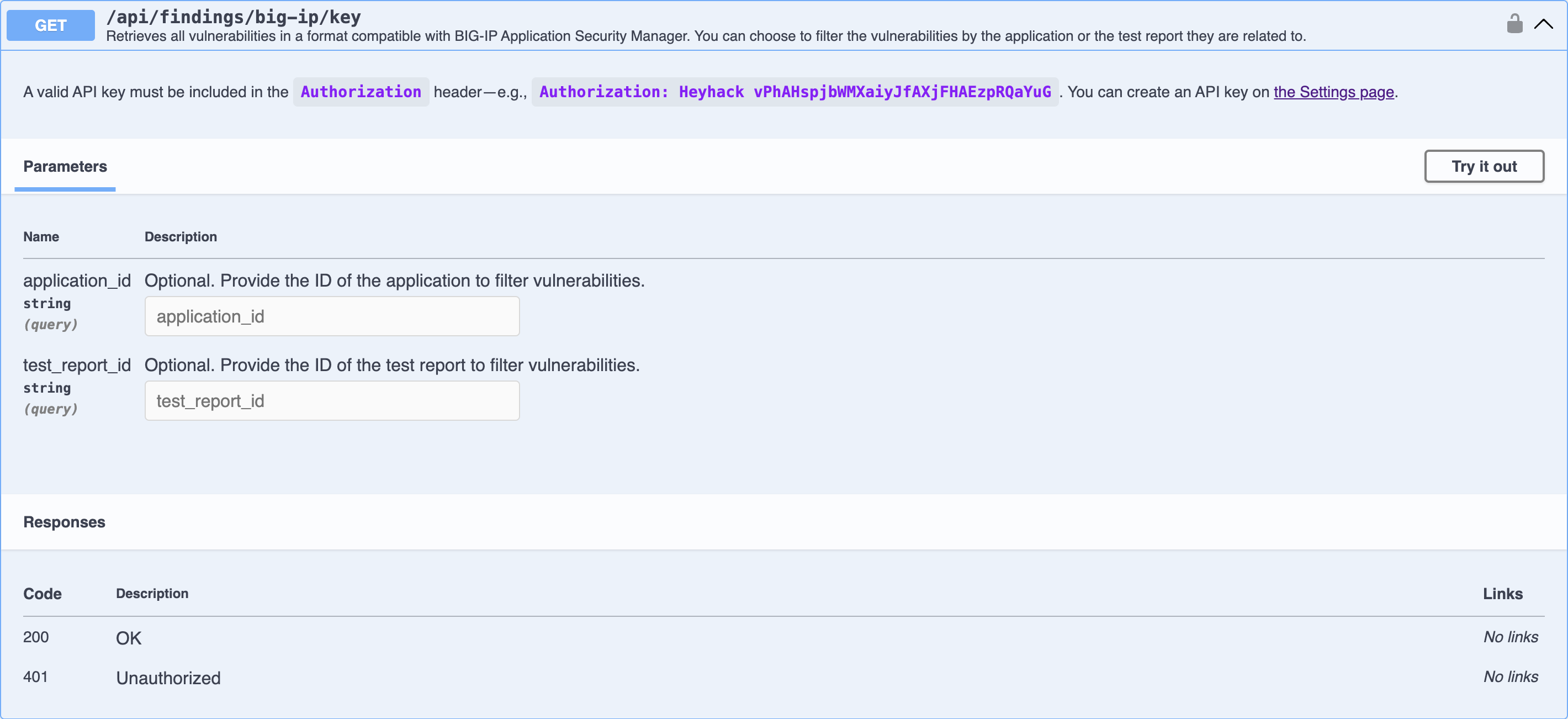
Figure: Export Vulnerabilities via API
As an example, you can use the following curl command to export vulnerabilities for a specific test report. Make sure to replace <TEST_REPORT_ID> with the actual ID of your test report and <API_KEY> with your API key.
curl --location 'https://app.heyhack.com/api/findings/big-ip/key?test_report_id=<TEST_REPORT_ID>' \ --header 'Authorization: Heyhack <API_KEY>'Below, you can find a sample response from the API:
<?xml version="1.0" encoding="utf-8"?><scanner_vulnerabilities xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema" version="1.0"> <vulnerability> <attack_type>SQL-Injection</attack_type> <name>SQL Injection</name> <url>https://juice.heywhack.com/rest/products/search?q=1%27</url> <parameter>q</parameter> <threat>critical</threat> <score>10</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Cross Site Scripting (XSS)</attack_type> <name>Cross-site Scripting (Reflected)</name> <url>https://juice.heywhack.com/#/search?q='%3E%22%3Ehh%3Cimg%20src%3Da%20onerror%3Dalert(962366646)%3E962366646</url> <parameter>q</parameter> <threat>critical</threat> <score>9</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Cross-site Request Forgery</attack_type> <name>Cross-site Request Forgery (CSRF)</name> <url>https://juice.heywhack.com/profile/image/file</url> <threat>medium</threat> <score>5</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Cross-site Request Forgery</attack_type> <name>Cross-site Request Forgery (CSRF)</name> <url>https://juice.heywhack.com/socket.io/?EIO=4&transport=polling&t=PUMhW8Q&sid=TKwNRkKtaXyCsq8sBngq</url> <threat>medium</threat> <score>5</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Cross-site Request Forgery</attack_type> <name>Cross-site Request Forgery (CSRF)</name> <url>https://juice.heywhack.com/rest/user/login</url> <threat>medium</threat> <score>5</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <name>Insecure Transport Layer</name> <url>https://juice.heywhack.com/</url> <threat>medium</threat> <score>5</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <name>Insecure Transport Layer</name> <url>https://juice.heywhack.com/</url> <threat>medium</threat> <score>4</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Set-Cookie does not use Secure keyword</attack_type> <name>Cookie without Secure Flag</name> <url>https://juice.heywhack.com/#/score-board</url> <cookie>code-fixes-component-format</cookie> <threat>low</threat> <score>4</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Set-Cookie does not use Secure keyword</attack_type> <name>Cookie without Secure Flag</name> <url>https://juice.heywhack.com/#/login</url> <cookie>token</cookie> <threat>low</threat> <score>4</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Set-Cookie does not use Secure keyword</attack_type> <name>Cookie without Secure Flag</name> <url>https://juice.heywhack.com/#/</url> <cookie>welcomebanner_status</cookie> <threat>low</threat> <score>4</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Set-Cookie does not use Secure keyword</attack_type> <name>Cookie without Secure Flag</name> <url>https://juice.heywhack.com/#/</url> <cookie>cookieconsent_status</cookie> <threat>low</threat> <score>4</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability> <vulnerability> <attack_type>Set-Cookie does not use Secure keyword</attack_type> <name>Cookie without Secure Flag</name> <url>https://juice.heywhack.com/#/</url> <cookie>language</cookie> <threat>low</threat> <score>4</score> <status>open</status> <opened xsi:nil="true" /> </vulnerability></scanner_vulnerabilities>For further details on how to make use of our API, please refer to the API documentation.
Support
For further assistance, please contact our support team.