Hello, Cloud!
On This Page:
- Prerequsites
- AWS Credentials for Terraform
- Step 1: Associating resource access policies to user
- Step 2: Creating a resource specific access policy (EC2 example below)
- Step 3: Create a secret access key for an IAM user.
- Deployment Types
- Volterra Quickstart (Install EKS and Node)
- Deployment Volterra Quickstart
- Destroy
- BYOK (Bring your own Kubernetes) and Volterra Node
- Destroy
- Volterra Concepts
This “Hello, Clouds!” is the second quickstart in Volterra’s “Hello, World!” series. It will start by deploying an application in AWS using EKS (Elastic Kubernetes Service) with VoltMesh acting as Ingress/Egress gateway. Alternatively, users can bring their existing EKS cluster and deploy only VoltMesh as Ingress/Egress gateway. The workflow walks through the steps of discovering services on EKS through VoltMesh and use VoltConsole for observability.
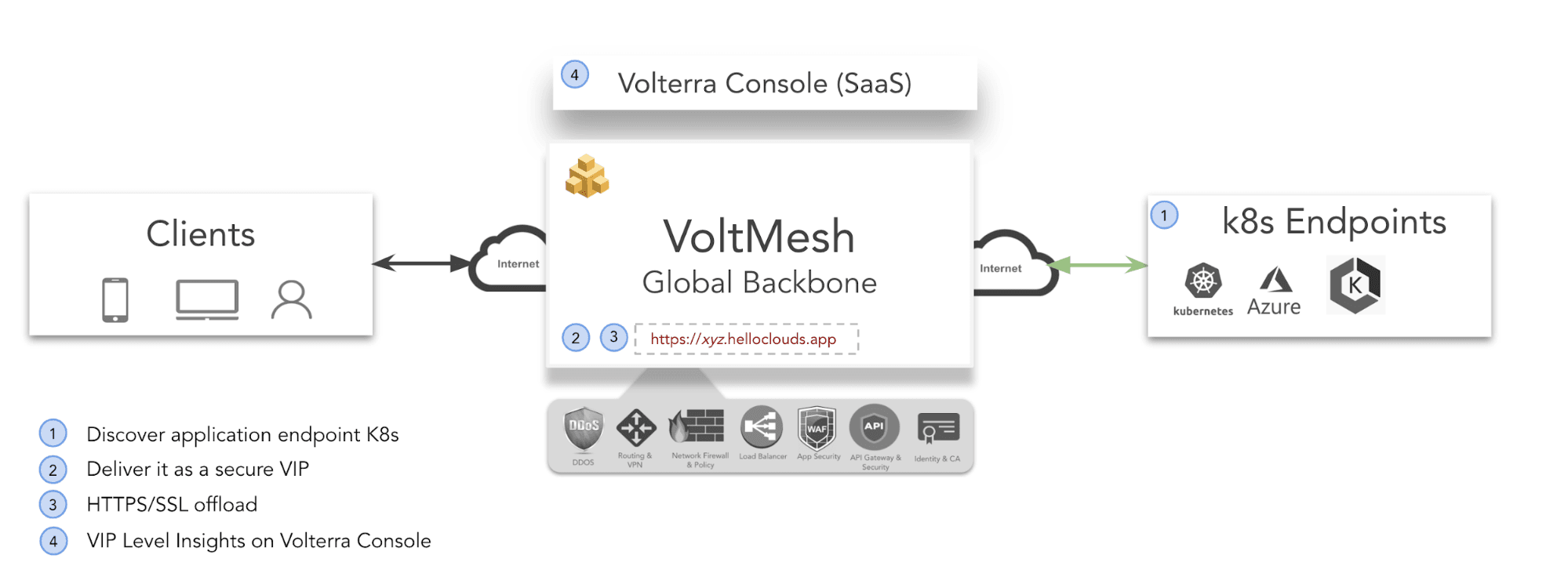
In summary, you will:
- Discover a web application running on EKS using Volterra Load Balancing and Service Mesh.
- Securely deliver it across the Internet using Volterra’s Secure Backbone.
- Protect against application attacks using Volterra’s Application Security.
- Get host-level insights via VoltConsole.
Prerequsites
-
Note: If you don’t have an account please Sign-Up.
-
EKS cluster with atleast one node on AWS.
Note: If you don’t have an existing EKS service running on AWS, the guide walks through setting up one.
-
AWS access/secret keys for an IAM user with api-permissions to access EC2, VPC and other related services.
Note: If you don’t have a Key already setup, follow the instructions below to configure the same.
-
For more information:
AWS Credentials for Terraform
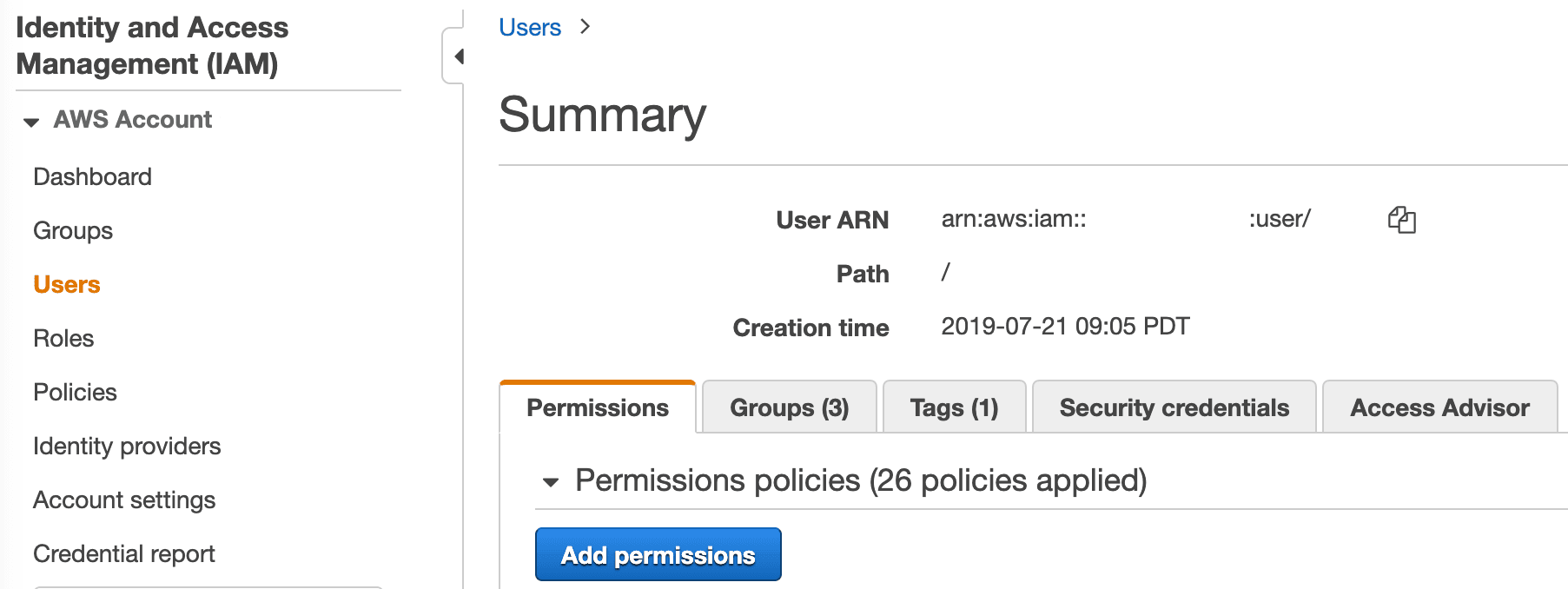
Step 1: Associating resource access policies to user
Open the IAM console. Click ‘Users’ in the ‘Details’ pane, click the appropriate IAM user, from the ‘Permissions’ tab choose ‘Add permissions’ to associate required policies to the user. Users can choose existing policies or create one. User should attach policies like
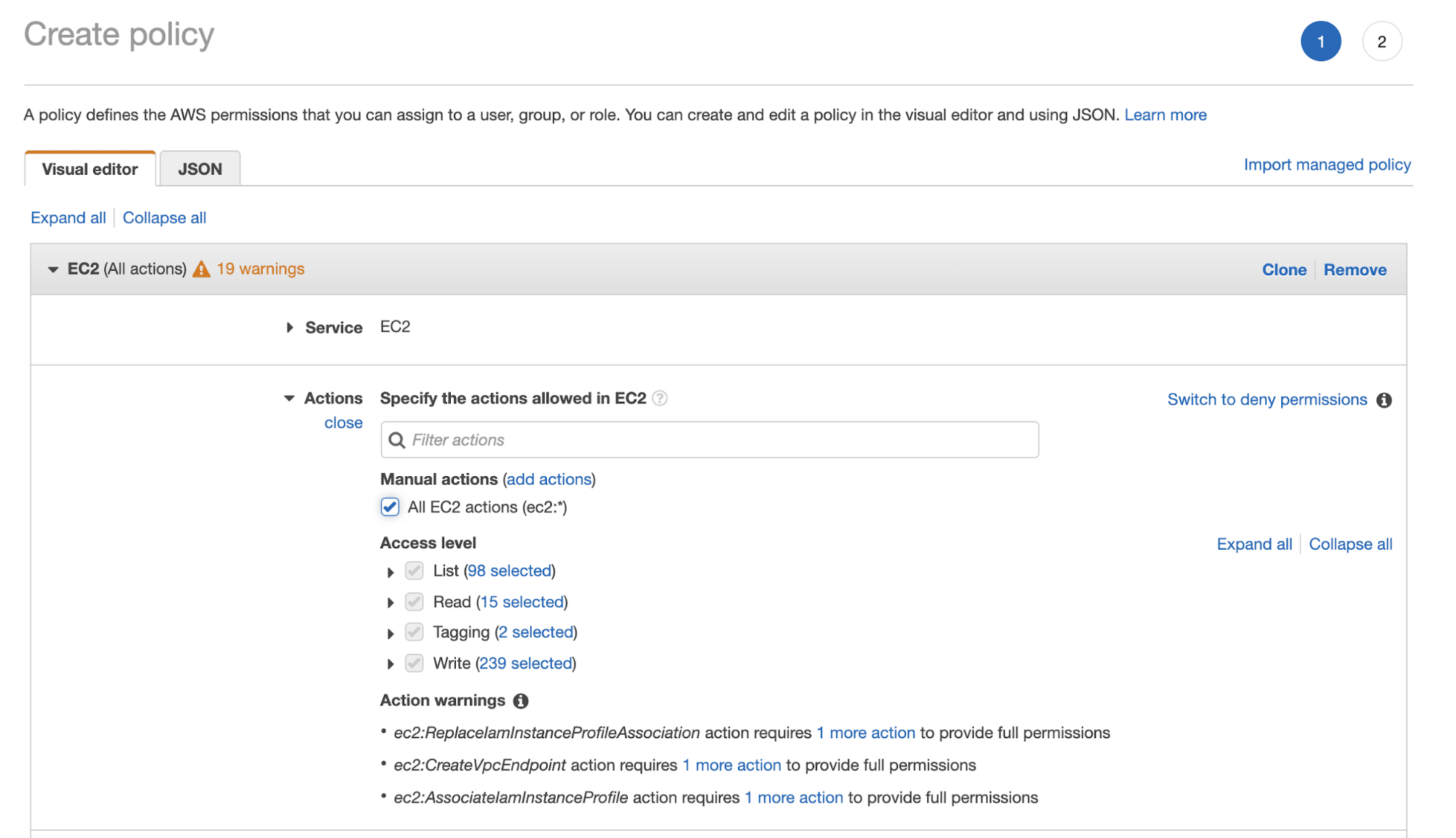
Step 2: Creating a resource specific access policy (EC2 example below)
Open the IAM console. Click ‘Users’ in the ‘Details’ pane. From the ‘Policies’ section use ‘create policy’ to define a new policy.
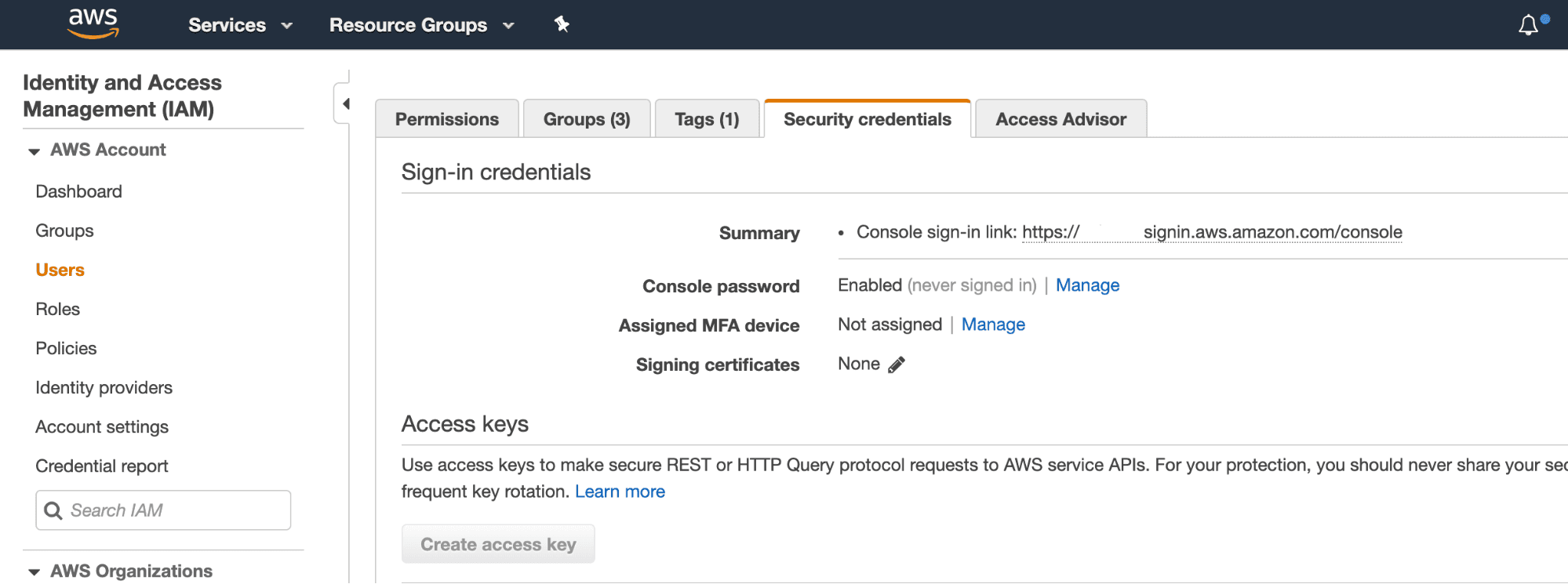
Step 3: Create a secret access key for an IAM user.
Open the IAM console. Click ‘Users’ in the ‘Details’ pane, click the appropriate IAM user,from the ‘Security Credentials’ tab choose ‘Create access key’ to create a new access key for IAM user (this step yields a .csv file with access key and secret key).
Deployment Types
There are two deployment types:
- Volterra Quickstart (Install EKS and Node)
- BYOK (Bring your own Kubernetes)
Volterra Quickstart (Install EKS and Node)
Using Volterra Quick Start Tool, deploy a new EKS cluster and Volterra Node and connect it to VoltMesh
- Follow these sequence of steps to
- Create an EKS cluster
- Install Volterra node or cluster (on EC2 VM)
- Provision required Volterra objects for service Discovery.
Deployment Volterra Quickstart
Step 1: Download and save your PCKS file (.p12) with your API credentials from your Volterra tenant.
- Don’t have your file? See Getting Started with VES.
Step 2: Create a terraform variable file. Below is a sample input file.
Sample aws.tfvars
# DEFINITIONS
#
# access_key: IAM user access_key (or) root access_key
# secret_key: IAM user secret_key (or) root secret_key
# machine_public_key: Public key to ssh to the machine
# machine_image: Volterra Image
# deployment: AWS deployment name
# region: AWS Region
# eks_worker_vm_count: Number of Worker Nodes
# api_creds_p12: \$PATH/to_your_api_creds.p12
# tenant_name: VES Tenant Name
# namespace: VES Namespace
# https_offload: CERT hosting/SSL termination (true|false)
# discovery_object_name : VES Discovery Object Name (created in system namespace) - default: quickstart-discovery
# endpoint_name: VES Endpoint Name - default: quickstart-endpoint
# cluster_name: VES Cluster Name - default: quickstart-cluster
# route_name: VES Route Name - default: quickstart-route
# advertise_policy_name: VES Advertise Policy Name - default: quickstart-adv-policy
# virtual_host_name: VES Virtual Host Name - default: quickstart-vhost
# domain: VES Domain Name configured in Virtual Host
# kubernetes_service_name: Kubernetes service with bookinfo-web endpoint - default: productpage
# kubernetes_service_namespace: Namespace in which bookinfo application is deployed - default: bookinfo
{
"access_key": "<aws_Access_key>",
"secret_key": "<aws_Secret_key>",
"machine_public_key": "<ssh-pub-key>",
"machine_image": "<ami-id>",
"deployment": "<deployment-name>",
"region": "us-east-2",
"eks_cluster": true,
"eks_worker_vm_count": "<worker_node_vm_count>",
"api_creds_p12": "/home/user1/Api_Credentials.p12",
"tenant_name": "smart-retail",
"namespace": "quickstart2",
"discovery_object_name": "quickstart-discovery",
“https_offload”: “<true/false>”,
"endpoint_name": "quickstart-endpoint",
"kubernetes_service_name": "productpage",
"kubernetes_service_namespace": "bookinfo",
"cluster_name": "quickstart-cluster",
"route_name": "quickstart-route",
"advertise_policy_name": "quickstart-adv-policy",
"virtual_host_name": "quickstart-vhost",
"domain": "hello-cloud.volterra.io"
}
Step 3: Download Volterra Quickstart Script deployment script to the local machine.
docker run --rm -v \$(pwd):/opt/bin:rw volterraio/volt-terraform:latest cp /deploy-terraform.sh .
Step 4: Run the deploy-terraform.sh to discover, connect and secure through VoltMesh. This will perform the following sequence of steps:
- Creates an EKS Cluster with nodes specified in terraform input variables file.
- Creates VoltMesh objects and connects to EKS cluster created in Step 1.
- Deploys the sample application on EKS (Kubernetes) cluster created in Step 1.
- Configures the Discovery Object.
- Configures Endpoint, cluster, route, advertise Policy, and virtual host objects.
./deploy-terraform.sh apply -i <absolute_path_to_variable_file> -tn example/hello-clouds --force
Step 5: Verify the EKS cluster is up and running.
echo "\$(terraform output eks_kubeconfig)" > ./k8s_config
export KUBECONFIG=./k8s_config
kubectl get nodes
Step 6: Verify if the bookinfo application is deployed and functional on EKS cluster.
kubectl get pods,svc
A successful output shows all pod status as up and running. A sample output is shown below:
\$ kubectl get pods,svc
NAME READY STATUS RESTARTS AGE
pod/details-v1-68fbb76fc-9hztq 2/2 Running 0 42s
pod/productpage-v1-6c6c87ffff-prf27 2/2 Running 0 42s
pod/ratings-v1-7bdfd65ccc-gvcf5 2/2 Running 0 42s
pod/reviews-v1-5c5b7b9f8d-7w6cm 2/2 Running 0 42s
pod/reviews-v2-569796655b-7swqg 2/2 Running 0 42s
pod/reviews-v3-844bc59d88-smjvj 2/2 Running 0 42s
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/details ClusterIP 10.100.27.133 <none> 9080/TCP 42s
service/kubernetes ClusterIP 10.100.0.1 <none> 443/TCP 52d
service/productpage ClusterIP 10.100.146.75 <none> 9080/TCP 42s
service/ratings ClusterIP 10.100.206.181 <none> 9080/TCP 42s
service/release-name-smi-metrics ClusterIP 10.100.189.44 <none> 443/TCP 7d11h
service/reviews ClusterIP 10.100.77.44 <none>
Step 7: Open bookinfo web page in the browser using the domain provided in the variable file above.
open \$(./deploy-terraform.sh output -i <absolute_path_to_variable_file> terraform output exposed_dns)
Step 8: Generate client traffic to bookinfo application for VoltConsole dashboard statistics.
XYZ
Step 9: Open VoltConsole for bookinfo application statistics.
b. Note: It will take a few minutes for statistics to show up.
open \$(./deploy-terraform.sh output -i <absolute_path_to_variable_file> terraform output exposed_dns)
Destroy
Step 1: To destroy all Volterra service objects created then run the following:
./deploy-terraform.sh destroy -i <absolute_path_to_vars_file> -tn example/quickstart1 --force
BYOK (Bring your own Kubernetes) and Volterra Node
Deploy an application or an already existing application running on an EKS cluster, install Volterra Node and connect it to VoltMesh.
Note: For specific integration to other Kubernetes Service Discovery please see our installation & integration section.
-
Follow these sequence of steps to
- Install Volterra Node or Cluster (on EC2 VM)
- Provision required Volterra Objects for Service Discovery for service endpoints.
Deployment BYOK
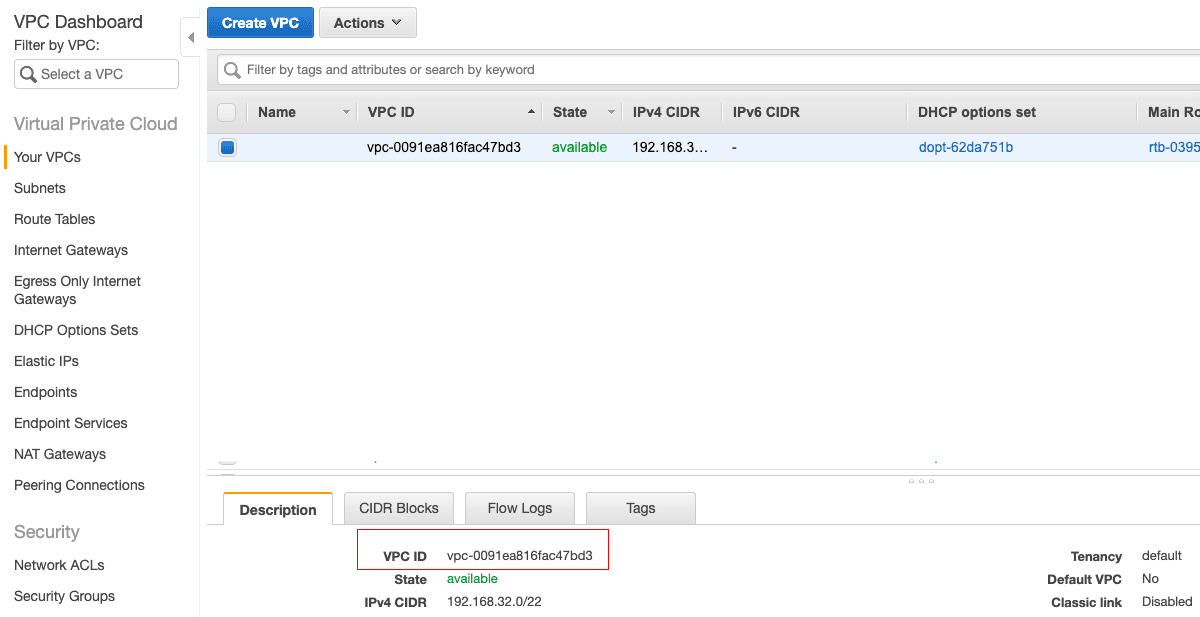
Step 1: Deploying VoltMesh to existing EKS requires VPC_ID in which existing EKS cluster is deployed. VPC_ID can be obtained from selecting ‘VPC’ in ‘Services’ and selecting the ‘VPC’ in which EKS is deployed.
Note: Volterra also enables users to deploy VoltMesh component in totally different VPC, this requires vpc-peering configuration which is not covered in this section.
- Don’t have your file? See Volterra Onboarding.
Step 2: Download and save your PCKS file (.p12) with your API credentials from your Volterra tenant.
Step 3: Create a terraform variable file. Below is a sample file. Sample aws.tfvars
# DEFINITIONS
#
# access_key: IAM user access_key (or) root access_key
# secret_key: IAM user secret_key (or) root secret_key
# machine_public_key: Public key to ssh to the machine
# machine_image: Volterra Image
# deployment: AWS deployment name
# region: AWS Region # Same Region as EKS Cluster
# vpc_id: AWS VPC # Same VPC as EKS Cluster
# api_creds_p12: \$PATH/to_your_api_creds.p12
# tenant_name: VES Tenant Name
# namespace: VES Namespace
# https_offload: CERT hosting/SSL termination (true|false)
# discovery_object_name : VES Discovery Object Name (created in system namespace)
# endpoint_name: VES Endpoint Name
# cluster_name: VES Cluster Name
# route_name: VES Route Name
# advertise_policy_name: VES Advertise Policy Name
# virtual_host_name: VES Virtual Host Name
# domain: VES Domain Name configured in Virtual Host
{
"access_key": "<aws_Access_key>",
"secret_key": "<aws_Secret_key>",
"machine_public_key": "<ssh-pub-key>",
"machine_image": "<ami-id>",
"deployment": "<deployment-name>",
"vpc_id": "<vpc_id>",
"region": "us-east-2",
"eks_cluster": false,
"eks_worker_vm_count": "<worker_node_vm_count>",
"api_creds_p12": "/home/user1/Api_Credentials.p12",
"tenant_name": "smart-retail",
"namespace": "quickstart1",
"discovery_object_name": "example1",
“https_offload”: “<true/false>”,
"endpoint_name": "example1",
"kubernetes_service_name": "Name of Kubernetes Service" (service to be discovered),
"kubernetes_service_namespace": "Namespace in which above Kubernetes Service is deployed",
"cluster_name": "example1",
"route_name": "example1",
"advertise_policy_name": "example1",
"virtual_host_name": "example1",
"domain": "example1.volterra.io"
}
Step 3: Download Volterra Quickstart Script deployment script to the local machine.
docker run --rm -v \$(pwd):/opt/bin:rw volterraio/volt-terraform:latest cp /deploy-terraform.sh .
Step 4: Run the deploy-terraform.sh to discover, connect and secure through VoltMesh. This will perform the following sequence of steps:
- Creates a EKS Cluster with nodes specified in variable file above
- Creates VoltMesh objects and connects to EKS cluster created in (1).
- Deploy as sample bookinfo application on EKS (Kubernetes) cluster created above
- Configures the Discovery Object
- Configures Endpoint, Cluster, Route, Advertise Policy and Virtual Host Objects
./deploy-terraform.sh apply -i <absolute_path_to_variable_file> -tn example/hello-clouds --force
Step 5: Verify the EKS cluster is up and running.
echo "\$(terraform output eks_kubeconfig)" > ./k8s_config
export KUBECONFIG=./k8s_config
kubectl get nodes
Step 6: Verify if the bookinfo application is deployed and functional on EKS cluster.
kubectl get pods,svc
A successful output shows all pod status as up and running. A sample output is shown below:
\$ kubectl get pods,svc
NAME READY STATUS RESTARTS AGE
pod/details-v1-68fbb76fc-9hztq 2/2 Running 0 42s
pod/productpage-v1-6c6c87ffff-prf27 2/2 Running 0 42s
pod/ratings-v1-7bdfd65ccc-gvcf5 2/2 Running 0 42s
pod/reviews-v1-5c5b7b9f8d-7w6cm 2/2 Running 0 42s
pod/reviews-v2-569796655b-7swqg 2/2 Running 0 42s
pod/reviews-v3-844bc59d88-smjvj 2/2 Running 0 42s
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/details ClusterIP 10.100.27.133 <none> 9080/TCP 42s
service/kubernetes ClusterIP 10.100.0.1 <none> 443/TCP 52d
service/productpage ClusterIP 10.100.146.75 <none> 9080/TCP 42s
service/ratings ClusterIP 10.100.206.181 <none> 9080/TCP 42s
service/release-name-smi-metrics ClusterIP 10.100.189.44 <none> 443/TCP 7d11h
service/reviews ClusterIP 10.100.77.44 <none>
Step 7: Open bookinfo web page in the browser using the domain provided in the variable file above.
open \$(./deploy-terraform.sh output -i <absolute_path_to_variable_file> terraform output exposed_dns)
Step 8: Generate client traffic to bookinfo application for VoltConsole dashboard statistics.
XYZ
Step 9: Open VoltConsole for bookinfo application statistics.
Note: It will take a few minutes for statistics to show up.
open \$(./deploy-terraform.sh output -i <absolute_path_to_variable_file> terraform output exposed_dns)
Destroy
Step 1: To destroy all Volterra service objects created then run the following:
./deploy-terraform.sh destroy -i <absolute_path_to_vars_file> -tn example/quickstart1 --force

